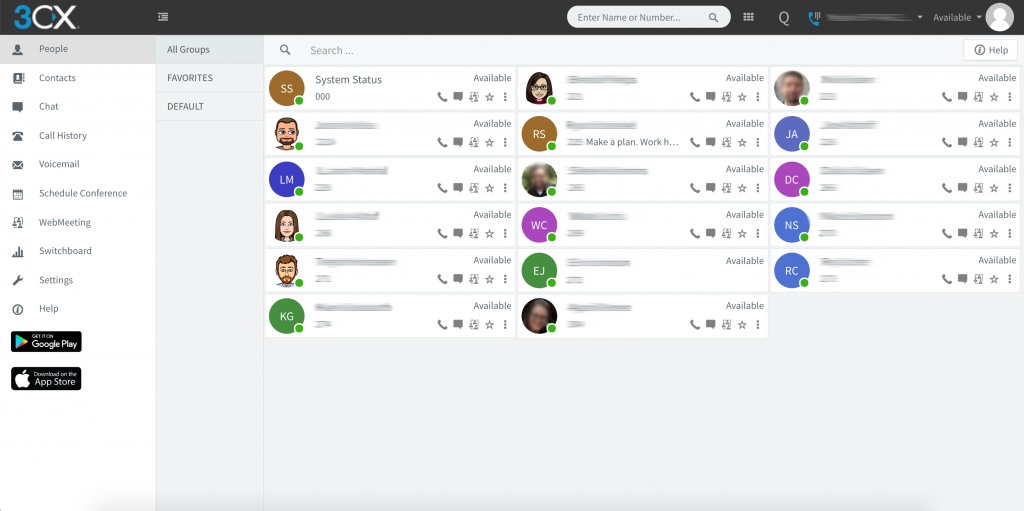
Logging In Go to your Web Client URL (sent to you in 3CX welcome email). Log in using your credentials (found in 3CX welcome email). Make, Receive & Transfer Calls Make a call by clicking on an extension or searching for name/number in the search box. Toggle the phone icon to make a call on […]
Featured
Was the invention of the QWERTY keyboard a marketing ploy?
There is a lot of speculation that goes in to why the QWERTY keyboard was invented. Some say that the QWERTY keyboard was originally designed to slow down typing speeds in order to prevent the mechanical lock up of the strikers. Typewriters with keys in alphabetical order often experienced this issue due to the close […]
Email Threats: Fake Receipt
Unfortunately, attempts to steal data are oftem found in phishing attempts sent directly to our personal inboxes. Levels of sophistication can vary from attempt to attempt. In this phishing attempt, the email was sent from someone that claimed to be “iCloud.” A closer look at the sender’s email address sends red flags to the careful […]
Edge Computing
What is edge computing? Edge computing is when processes are performed locally on the “edge” of the network making the amount of long-distance communication limited and communication between devices happen more quickly. Instead of devices exclusively communicating with the cloud, they communicate with their own, local servers/computers first. This reduces the amount of data being […]
Recovery After a Disaster
Whether it’s a fire, a natural disaster, human error or cyberattack, it is important to respond to a disaster in the best way possible. Every hour of downtime is crucial to the recovery of a business. Business continuity plans exist to help get the business up and running as soon as possible after a disaster. […]